A severe security vulnerability in a popular video calling software development kit (SDK) could have allowed an attacker to spy on ongoing private video and audio calls.
That’s according to new research published by the McAfee Advanced Threat Research (ATR) team today, which found the aforementioned flaw in Agora.io’s SDK used by several social apps such as eHarmony, Plenty of Fish, MeetMe, and Skout; healthcare apps like Talkspace, Practo, and Dr. First’s Backline; and in the Android app that’s paired with “temi” personal robot.
California-based Agora is a video, voice, and live interactive streaming platform, allowing developers to embed voice and video chat, real-time recording, interactive live streaming, and real-time messaging into their apps. The company’s SDKs are estimated to be embedded into mobile, web, and desktop applications across more than 1.7 billion devices globally.
McAfee disclosed the flaw (CVE-2020-25605) to Agora.io on April 20, 2020, following which the company released a new SDK on December 17, 2020, to remediate the threat posed by the vulnerability.
The security weakness, which is the consequence of incomplete encryption, could have been leveraged by bad actors to launch man-in-the-middle attacks and intercept communications between two parties.
“Agora’s SDK implementation did not allow applications to securely configure the setup of video/audio encryption, thereby leaving a potential for hackers to snoop on them,” the researchers said.
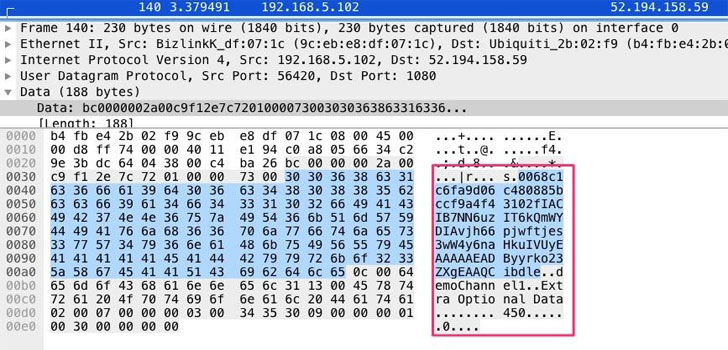
Specifically, the function responsible for connecting an end-user to a call passed parameters such as App ID and authentication token parameter in plaintext, thereby allowing an attacker to abuse this shortcoming to sniff network traffic so as to gather call information and subsequently launch their own Agora video application to dial into calls without the attendees’ knowledge stealthily.
Although there’s no evidence that the vulnerability was exploited in the wild, the development once again underscores the need for securing applications to safeguard user privacy.
“In the world of online dating, a breach of security or the ability to spy on calls could lead to blackmail or harassment by an attacker,” the researchers concluded. “Other Agora developer applications with smaller customer bases, such as the temi robot, are used in numerous industries such as hospitals, where the ability to spy on conversations could lead to the leak of sensitive medical information.”
It’s highly recommended that developers using Agora SDK upgrade to the latest version to mitigate the risk.