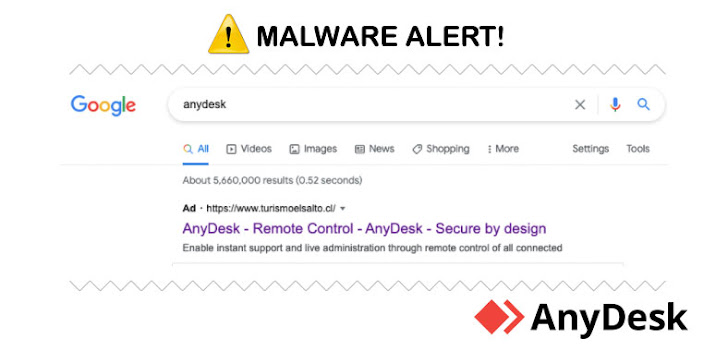
Cybersecurity researchers on Wednesday publicized the disruption of a “clever” malvertising network targeting AnyDesk that delivered a weaponized installer of the remote desktop software via rogue Google ads that appeared in the search engine results pages.
The campaign, which is believed to have begun as early as April 21, 2021, involves a malicious file that masquerades as a setup executable for AnyDesk (AnyDeskSetup.exe), which, upon execution, downloads a PowerShell implant to amass and exfiltrate system information.
“The script had some obfuscation and multiple functions that resembled an implant as well as a hardcoded domain (zoomstatistic[.]com) to ‘POST’ reconnaissance information such as user name, hostname, operating system, IP address and the current process name,” researchers from Crowdstrike said in an analysis.
AnyDesk’s remote desktop access solution has been downloaded by more than 300 million users worldwide, according to the company’s website. Although the cybersecurity firm did not attribute the cyber activity to a specific threat actor or nexus, it suspected it to be a “widespread campaign affecting a wide range of customers” given the large user base.
The PowerShell script may have all the hallmarks of a typical backdoor, but it’s the intrusion route where the attack throws a curve, signaling that it’s beyond a garden-variety data gathering operation — the AnyDesk installer is distributed through malicious Google ads placed by the threat actor, which are then served to unsuspecting people who are using Google to search for ‘AnyDesk.’
The fraudulent ad result, when clicked, redirects users to a social engineering page that’s a clone of the legitimate AnyDesk website, in addition to providing the individual with a link to the trojanized installer.
CrowdStrike estimates that 40% of clicks on the malicious ad turned into installations of the AnyDesk binary, and 20% of those installations included follow-on hands-on-keyboard activity. “While it is unknown what percentage of Google searches for AnyDesk resulted in clicks on the ad, a 40% Trojan installation rate from an ad click shows that this is an extremely successful method of gaining remote access across a wide range of potential targets,” the researchers said.
The company also said it notified Google of its findings, which is said to have taken immediate action to pull the ad in question.
“This malicious use of Google Ads is an effective and clever way to get mass deployment of shells, as it provides the threat actor with the ability to freely pick and choose their target(s) of interest,” the researchers concluded.
“Because of the nature of the Google advertising platform, it can provide a really good estimate of how many people will click on the ad. From that, the threat actor can adequately plan and budget based on this information. In addition to targeting tools like AnyDesk or other administrative tools, the threat actor can target privileged/administrative users in a unique way.”