E-commerce platforms in the U.S., Germany, and France have come under attack from a new form of malware that targets Nginx servers in an attempt to masquerade its presence and slip past detection by security solutions.
“This novel code injects itself into a host Nginx application and is nearly invisible,” Sansec Threat Research team said in a new report. “The parasite is used to steal data from eCommerce servers, also known as ‘server-side Magecart.'”
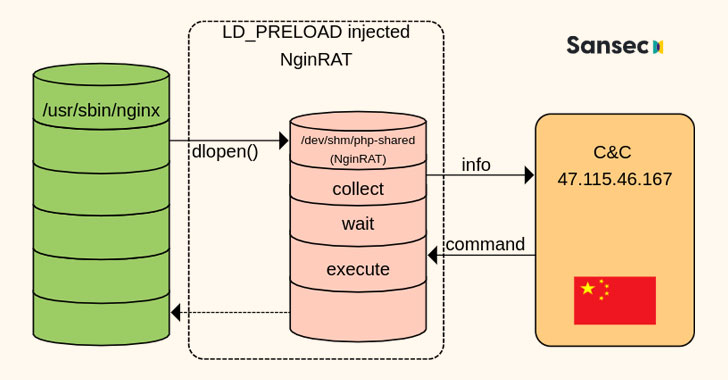
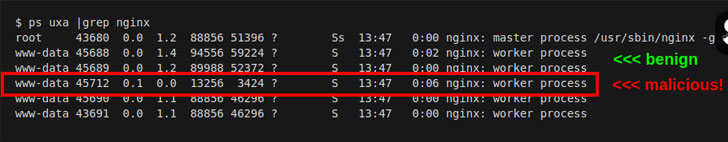
A free and open-source software, Nginx is a web server that can also be used as a reverse proxy, load balancer, mail proxy, and HTTP cache. NginRAT, as the advanced malware is called, works by hijacking a host Nginx application to embed itself into the webserver process.
The remote access trojan itself is delivered via CronRAT, another piece of malware the Dutch cybersecurity firm disclosed last week as hiding its malicious payloads in cron jobs scheduled to execute on February 31st, a non-existent calendar day.
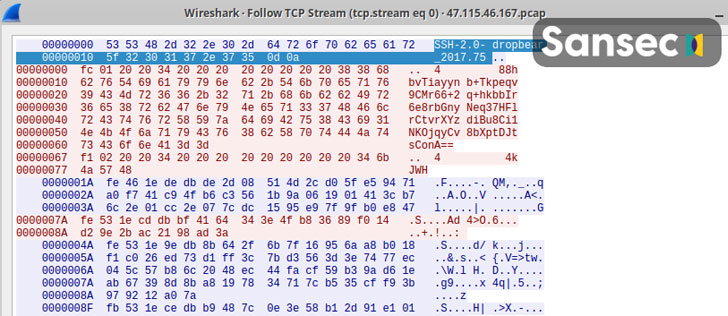
Both CronRAT and NginRAT are designed to provide a remote way into the compromised servers, and the goal of the intrusions is to make server-side modifications to the compromised e-commerce websites in a manner that enable the adversaries to exfiltrate data by skimming online payment forms.
The attacks, collectively known as Magecart or web skimming, are the work of a cybercrime syndicate comprised of dozens of subgroups that are involved in digital credit card theft by exploiting software vulnerabilities to gain access to an online portal’s source code and insert malicious JavaScript code that siphons the data shoppers enter into checkout pages.
“Skimmer groups are growing rapidly and targeting various e-commerce platforms using a variety of ways to remain undetected,” Zscaler researchers noted in an analysis of the latest Magecart trends published earlier this year.
“The latest techniques include compromising vulnerable versions of e-commerce platforms, hosting skimmer scripts on CDNs and cloud services, and using newly registered domains (NRDs) lexically close to any legitimate web service or specific e-commerce store to host malicious skimmer scripts.”