A new kind of Windows NTLM relay attack dubbed DFSCoerce has been uncovered that leverages the Distributed File System (DFS): Namespace Management Protocol (MS-DFSNM) to seize control of a domain.
“Spooler service disabled, RPC filters installed to prevent PetitPotam and File Server VSS Agent Service not installed but you still want to relay [Domain Controller authentication to [Active Directory Certificate Services]? Don’t worry MS-DFSNM have (sic) your back,” security researcher Filip Dragovic said in a tweet.
MS-DFSNM provides a remote procedure call (RPC) interface for administering distributed file system configurations.
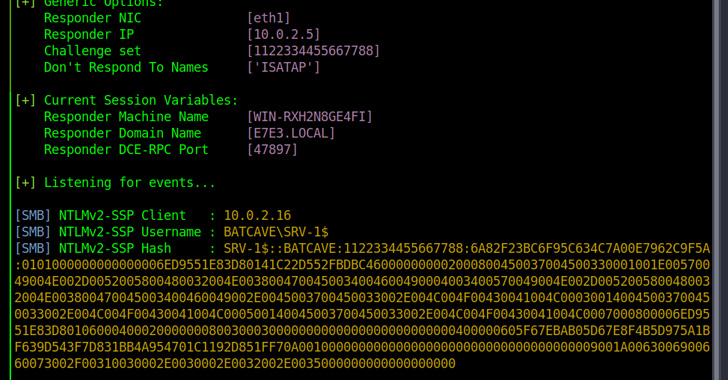
The NTLM (NT Lan Manager) relay attack is a well-known method that exploits the challenge-response mechanism. It allows malicious parties to sit between clients and servers and intercept and relay validated authentication requests in order to gain unauthorized access to network resources, effectively gaining an initial foothold in Active Directory environments.
The discovery of DFSCoerce follows a similar method called PetitPotam that abuses Microsoft’s Encrypting File System Remote Protocol (MS-EFSRPC) to coerce
Windows servers, including domain controllers, into authenticating with a relay under an attacker’s control, letting threat actors potentially take over an entire domain.
“By relaying an NTLM authentication request from a domain controller to the Certificate Authority Web Enrollment or the Certificate Enrollment Web Service on an AD CS system, an attacker can obtain a certificate that can be used to obtain a Ticket Granting Ticket (TGT) from the domain controller,” the CERT Coordination Center (CERT/CC) noted, detailing the attack chain.
To mitigate NTLM relay attacks, Microsoft recommends enabling protections like Extended Protection for Authentication (EPA), SMB signing, and turning off HTTP on AD CS servers.