Threat actors have been exploiting the newly disclosed zero-day flaw in Palo Alto Networks PAN-OS software dating back to March 26, 2024, nearly three weeks before it came to light yesterday.
The network security company’s Unit 42 division is tracking the activity under the name Operation MidnightEclipse, attributing it as the work of a single threat actor of unknown provenance.
The security vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.0), is a command injection flaw that enables unauthenticated attackers to execute arbitrary code with root privileges on the firewall.
It’s worth noting that the issue is applicable only to PAN-OS 10.2, PAN-OS 11.0, and PAN-OS 11.1 firewall configurations that have GlobalProtect gateway and device telemetry enabled.
Operation MidnightEclipse entails the exploitation of the flaw to create a cron job that runs every minute to fetch commands hosted on an external server (“172.233.228[.]93/policy” or “172.233.228[.]93/patch”), which are then executed using the bash shell.
The attackers are said to have manually managed an access control list (ACL) for the command-and-control (C2) server to ensure that it can only be accessed from the device communicating with it.
While the exact nature of the command is unknown, it’s suspected that the URL serves as a delivery vehicle for a Python-based backdoor on the firewall that Volexity – which discovered in-the-wild exploitation of CVE-2024-3400 on April 10, 2024 – is tracking as UPSTYLE and is hosted on a different server (“144.172.79[.]92” and “nhdata.s3-us-west-2.amazonaws[.]com”).
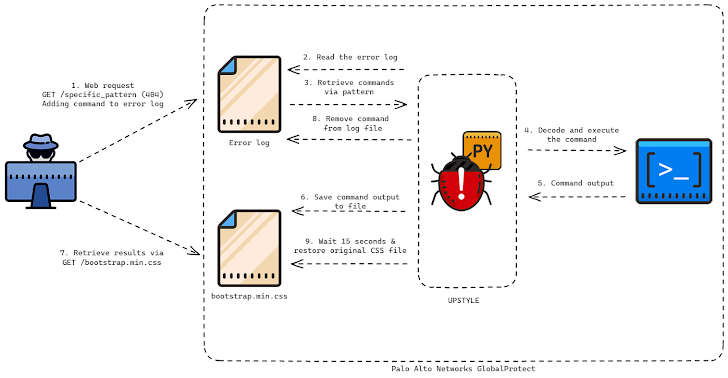
The Python file is designed to write and launch another Python script (“system.pth”), which subsequently decodes and runs the embedded backdoor component that’s responsible for executing the threat actor’s commands in a file called “sslvpn_ngx_error.log.” The results of the operation are written to a separate file named “bootstrap.min.css.”
The most interesting aspect of the attack chain is that both the files used to extract the commands and write the results are legitimate files associated with the firewall –
- /var/log/pan/sslvpn_ngx_error.log
- /var/appweb/sslvpndocs/global-protect/portal/css/bootstrap.min.css
As for how the commands are written to the web server error log, the threat actor forges specially crafted network requests to a non-existent web page containing a specific pattern. The backdoor then parses the log file and searches for the line matching the same regular expression (“img\[([a-zA-Z0-9+/=]+)\]”) to decode and run the command within it.
“The script will then create another thread that runs a function called restore,” Unit 42 said. “The restore function takes the original content of the bootstrap.min.css file, as well as the original access and modified times, sleeps for 15 seconds and writes the original contents back to the file and sets the access and modified times to their originals.”
The main goal appears to be to avoid leaving traces of the command outputs, necessitating that the results are exfiltrated within 15 seconds before the file is overwritten.
Volexity, in its own analysis, said it observed the threat actor remotely exploiting the firewall to create a reverse shell, download additional tooling, pivot into internal networks, and ultimately exfiltrate data. The exact scale of the campaign is presently unclear. The adversary has been assigned the moniker UTA0218 by the company.
“The tradecraft and speed employed by the attacker suggests a highly capable threat actor with a clear playbook of what to access to further their objectives,” the American cybersecurity firm said.
“UTA0218’s initial objectives were aimed at grabbing the domain backup DPAPI keys and targeting active directory credentials by obtaining the NTDS.DIT file. They further targeted user workstations to steal saved cookies and login data, along with the users’ DPAPI keys.”
Organizations are recommended to look for signs of lateral movement internally from their Palo Alto Networks GlobalProtect firewall device.
The development has also prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to add the flaw to its Known Exploited Vulnerabilities (KEV) catalog, requiring federal agencies to apply the patches by April 19 to mitigate potential threats. Palo Alto Networks is expected to release fixes for the flaw no later than April 14.
“Targeting edge devices remains a popular vector of attack for capable threat actors who have the time and resources to invest into researching new vulnerabilities,” Volexity said.
“It is highly likely UTA0218 is a state-backed threat actor based on the resources required to develop and exploit a vulnerability of this nature, the type of victims targeted by this actor, and the capabilities displayed to install the Python backdoor and further access victim networks.”