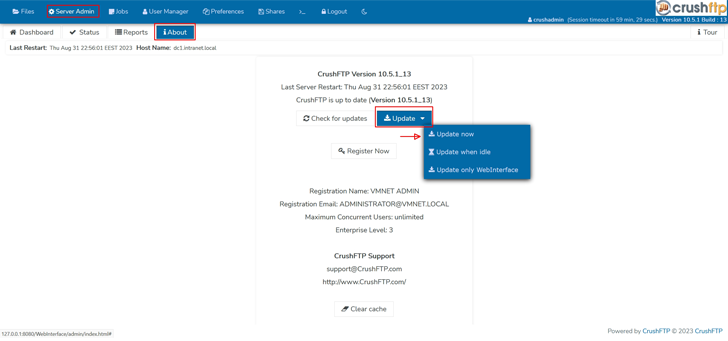
Users of the CrushFTP enterprise file transfer software are being urged to update to the latest version following the discovery of a security flaw that has come under targeted exploitation in the wild.
“CrushFTP v11 versions below 11.1 have a vulnerability where users can escape their VFS and download system files,” CrushFTP said in an advisory released Friday. “This has been patched in v11.1.0.”
That said, customers who are operating their CrushFTP instances within a DMZ (demilitarized zone) restricted environment are protected against the attacks.
Simon Garrelou of Airbus CERT has been credited with discovering and reporting the flaw. It has yet to be assigned a CVE identifier.
Cybersecurity company CrowdStrike, in a post shared on Reddit, said it has observed an exploit for the flaw being used in the wild in a “targeted fashion.”
These intrusions are said to have mainly targeted U.S. entities, with the intelligence gathering activity suspected to be politically motivated.
“CrushFTP users should continue to follow the vendor’s website for the most up-to-date instructions and prioritize patching,” CrowdStrike said.