Cybersecurity researchers, for the first time, may have found a potential connection between the backdoor used in the SolarWinds hack to a previously known malware strain.
In new research published by Kaspersky researchers today, the cybersecurity firm said it discovered several features that overlap with another backdoor known as Kazuar, a .NET-based malware first documented by Palo Alto Networks in 2017.
Disclosed early last month, the espionage campaign was notable for its scale and stealth, with the attackers leveraging the trust associated with SolarWinds Orion software to infiltrate government agencies and other companies so as to deploy a custom malware codenamed “Sunburst.”
Shared Features Between Sunburst and Kazuar
Attribution for the SolarWinds supply-chain compromise has been difficult in part due to little-to-no clues linking the attack infrastructure to previous campaigns or other well-known threat groups.
But Kaspersky’s latest analysis of the Sunburst backdoor has revealed a number of shared features between the malware and Kazuar, leading the researchers to suspect that —
- Both Sunburst and Kazuar were developed by the same threat group
- The adversary behind Sunburst used Kazuar as an inspiration
- The groups behind Kazuar (Turla) and Sunburst (UNC2452 or Dark Halo) obtained the malware from a single source
- The developers of Kazuar moved to another team, taking their toolset with them, or
- The Sunburst developers deliberately introduced these links as “false flag” to shift blame to another group
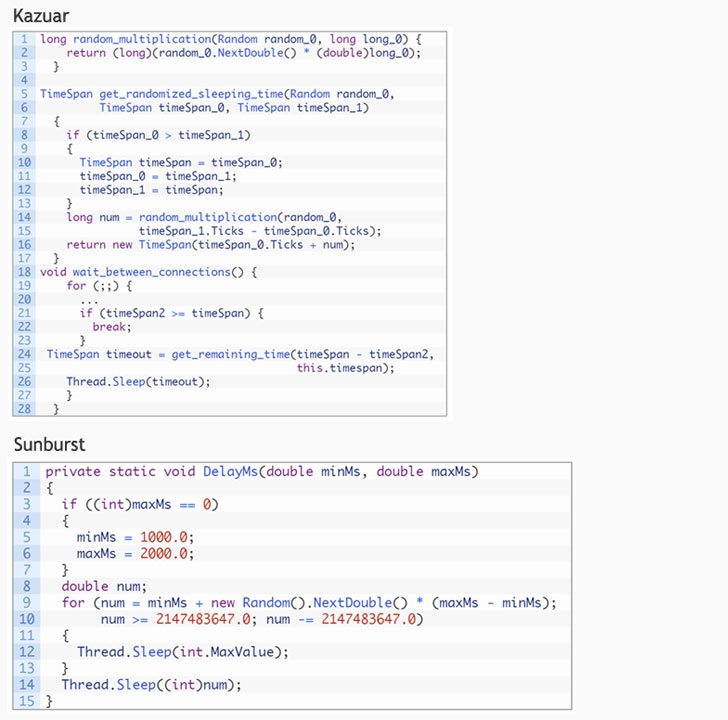
The commonalities shared between the two malware families include the use of a sleeping algorithm to stay dormant for a random period between connections to a C2 server, the extensive usage of the FNV-1a hash to obfuscate the malicious code, and the use of a hashing algorithm to generate unique victim identifiers.
While Kazuar randomly selects a sleeping period between two and four weeks between C2 connections, Sunburst randomly opts for a sleeping period between 12 and 14 days before contacting the server for initial reconnaissance. But researchers noted that the formula used to calculate the sleeping time remains the same.
Kazuar’s Possible Links to Turla
Kazuar is a fully featured backdoor written using the .NET Framework and relies on a command-and-control (C2) channel to allow actors to interact with the compromised system and exfiltrate data. Its features run the typical spyware gamut, with support for running malicious commands, capture screenshots, and even deploy additional functionalities via a plugin command.
Palo Alto Networks’ Unit 42 team tentatively linked the tool to the Russian threat group Turla (aka Uroburos and Snake) based on the fact that the “code lineage in Kazuar can be traced back to at least 2005.”
What’s more, on November 18, 2020, Kazuar appears to have undergone a complete redesign with a new keylogger and password-stealing functions added to the backdoor that’s implemented in the form of C2 server command.
While it’s normal for threat actors to keep updating their toolset and introduce features designed to bypass endpoint detection and response (EDR) systems, Kaspersky researchers raised the possibility that the changes may have been introduced in response to the SolarWinds breach.
“Suspecting the SolarWinds attack might be discovered, the Kazuar code was changed to resemble the Sunburst backdoor as little as possible,” the researchers said.
CISA Updates SolarWinds Advisory
Last week, the U.S. Cybersecurity and Infrastructure Security Agency (CISA), along with the Federal Bureau of Investigation (FBI), the Office of the Director of National Intelligence (ODNI), and the National Security Agency (NSA), issued a joint statement formally accusing an adversary “likely Russian in origin” for staging the SolarWinds hack.
Furthermore, CISA, in an update to its advisory on January 6, said, “incident response investigations have identified that initial access in some cases was obtained by password guessing, password spraying, and inappropriately secured administrative credentials accessible via external remote access services.”
“These code overlaps between Kazuar and Sunburst are interesting and represent the first potential identified link to a previously known malware family,” Kaspersky researchers concluded.
“While Kazuar and Sunburst may be related, the nature of this relation is still not clear. Through further analysis, it is possible that evidence confirming one or several of these points might arise. At the same time, it is also possible that the Sunburst developers were really good at their opsec and didn’t make any mistakes, with this link being an elaborate false flag.”