The threat actors behind the Hive ransomware-as-a-service (RaaS) scheme have launched attacks against over 1,300 companies across the world, netting the gang $100 million in illicit payments as of November 2022.
“Hive ransomware has targeted a wide range of businesses and critical infrastructure sectors, including government facilities, communications, critical manufacturing, information technology, and — especially — Healthcare and Public Health (HPH),” U.S. cybersecurity and intelligence authorities said in an alert.
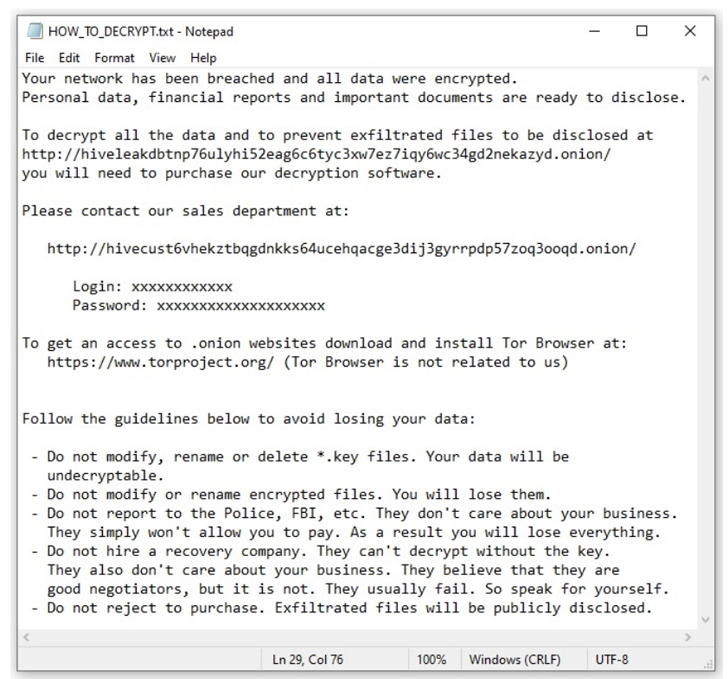
Active since June 2021, Hive’s RaaS operation involves a mix of developers, who create and manage the malware, and affiliates, who are responsible for conducting the attacks on target networks by often purchasing initial access from initial access brokers (IABs).
In most cases, gaining a foothold involves the exploitation of ProxyShell flaws in Microsoft Exchange Server, followed by taking steps to terminate processes associated with antivirus engines and data backups as well as delete Windows event logs.
The threat actor, which recently upgraded its malware to Rust as a detection evasion measure, is also known to remove virus definitions prior to encryption.
“Hive actors have been known to reinfect—with either Hive ransomware or another ransomware variant—the networks of victim organizations who have restored their network without making a ransom payment,” the U.S. Cybersecurity and Infrastructure Security Agency (CISA) said.
According to data shared by cybersecurity company Malwarebytes, Hive compromised about seven victims in August 2022, 14 in September, and two other entities in October, marking a drop in activity from July, when the group targeted 26 victims.