More than 8,000 domains and 13,000 subdomains belonging to legitimate brands and institutions have been hijacked as part of a sophisticated distribution architecture for spam proliferation and click monetization.
Guardio Labs is tracking the coordinated malicious activity, which has been ongoing since at least September 2022, under the name SubdoMailing. The emails range from “counterfeit package delivery alerts to outright phishing for account credentials.”
The Israeli security company attributed the campaign to a threat actor it calls ResurrecAds, which is known to resuscitate dead domains of or affiliated with big brands with the end goal of manipulating the digital advertising ecosystem for nefarious gains.
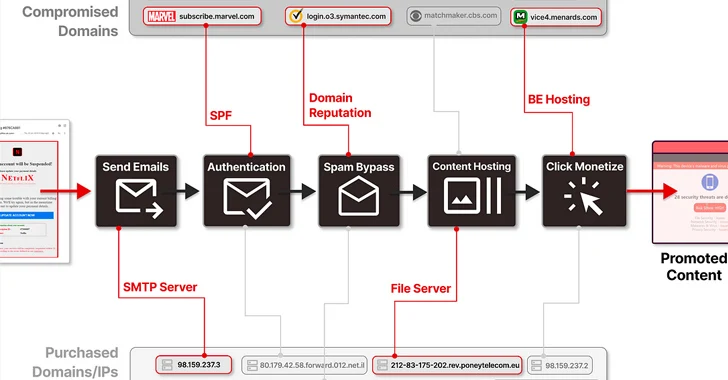
“‘ResurrecAds’ manages an extensive infrastructure encompassing a wide array of hosts, SMTP servers, IP addresses, and even private residential ISP connections, alongside many additional owned domain names,” security researchers Nati Tal and Oleg Zaytsev said in a report shared with The Hacker News.
In particular, the campaign “leverages the trust associated with these domains to circulate spam and malicious phishing emails by the millions each day, cunningly using their credibility and stolen resources to slip past security measures.”
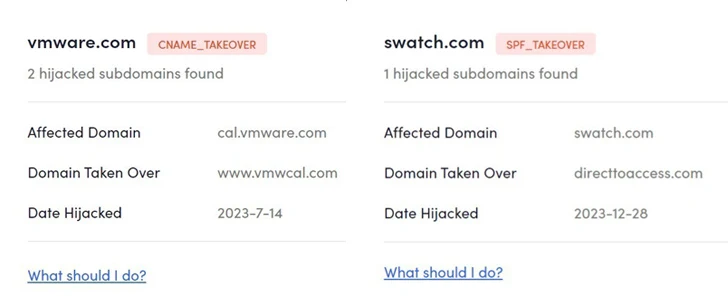
These subdomains belong to or are affiliated with big brands and organizations such as ACLU, eBay, Lacoste, Marvel, McAfee, MSN, Pearson, PwC, Swatch, Symantec, The Economist, UNICEF, and VMware, among
The campaign is notable for its ability to bypass standard security blocks, with the entire body conceived as an image to evade text-based spam filters, clicking which initiates a series of redirections through different domains.
“These redirects check your device type and geographic location, leading to content tailored to maximize profit,” the researchers explained.
“This could be anything from an annoying ad or affiliate link to more deceptive tactics like quiz scams, phishing sites, or even a malware download aimed at swindling you out of your money more directly.”
Another crucial aspect of these emails is that they are also capable of circumventing Sender Policy Framework (SPF), an email authentication method that’s designed to prevent spoofing by ensuring a mail server is authorized to send email for a given domain.
It’s not just SPF, as the emails also pass DomainKeys Identified Mail (DKIM) and Domain-based Message Authentication, Reporting and Conformance (DMARC) checks that help prevent messages from being marked as spam.
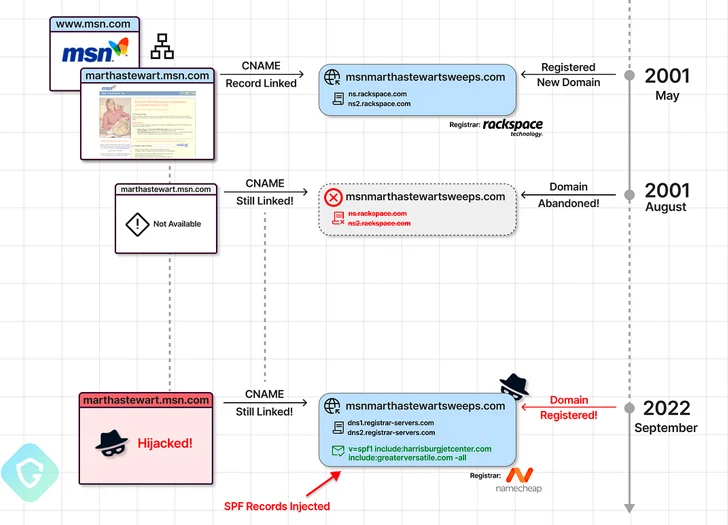
In one example of a deceptive cloud storage warning email highlighted by Guardio, the message originated from an SMTP server in Kyiv, yet was flagged as being sent from Return_UlKvw@marthastewart.msn.com.
A closer examination of the DNS record for marthastewart.msn.com revealed that the subdomain is linked to another domain (msnmarthastewartsweeps[.]com) by means of a CNAME record, an aliasing technique that has been previously weaponized by advertising technology companies to get around third-party cookie blocking.
“This means that the subdomain inherits the entire behavior of msnmarthastewartsweeps[.]com , including its SPF policy,” the researchers said. “In this case, the actor can send emails to anyone they wish as if msn[.]com and their approved mailers sent those emails!”
It’s worth pointing out here that both the domains were legitimate and briefly active at some point in 2001, before they were left in an abandoned state for 21 years. It wasn’t until September 2022 when msnmarthastewartsweeps[.]com was privately registered with Namecheap.
In other words, the sophisticated hijacking scheme entails the threat actors systematically scanning for long-forgotten subdomains with dangling CNAME records of abandoned domains and then registering them to take control of them.
CNAME-takeover can also have serious consequences when such reputed subdomains are seized to host bogus phishing landing pages designed to harvest users’ credentials. That said, there is no evidence that any of the hijacked subdomains have been used for this purpose.
Guardio said it also found instances where the DNS SPF record of a known domain holds abandoned domains associated with defunct email- or marketing-related services, thereby allowing attackers to grab ownership of such domains, inject their own IP addresses into the record, and ultimately send emails on behalf of the main domain name.
In an effort to counter the threat and dismantle the infrastructure, Guardio has made available a SubdoMailing Checker, a website that enables domain administrators and site owners to look for signs of compromise.
“This operation is meticulously designed to misuse these assets for distributing various malevolent ‘Advertisements,’ aiming to generate as many clicks as possible for these ‘ad network’ clients,” the researchers said.
“Armed with a vast collection of compromised reputable domains, servers, and IP addresses, this ad network deftly navigates through the malicious email propagation process, seamlessly switching and hopping among its assets at will.”